It was March 26, 1999. People were still adjusting to using email on a regular basis, and Microsoft Outlook had only been around for a few years. A man named David L. Smith decided to capitalize on the confusion surrounding the internet and email when he created the first successful email-aware computer virus. The malware — the Melissa virus — was one of the first to get public attention because it caused more than $80 million in damage.
Twenty years later, not-so-sweet Melissa, reportedly named after a Florida stripper Smith knew, is seen as a wakeup call with a silver lining. Computer users were shocked into awareness aware of their vulnerabilities — and forced some to reckon with those weaknesses.

How did it work?
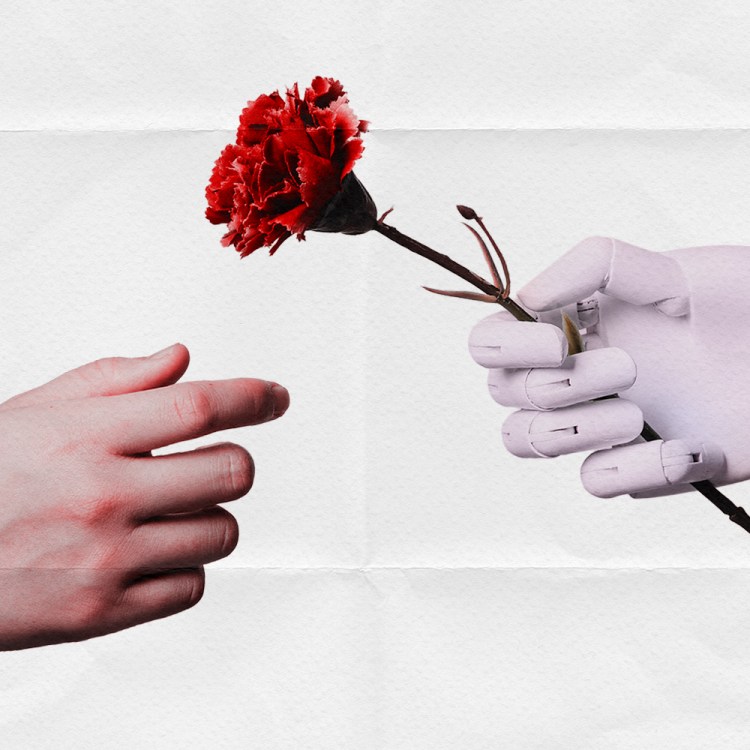
The Melissa virus, unlike infections that came later, did not damage individual computers, according to a BBC news report from 1999. Instead, the virus spread via infected Word documents. Disguised as an important message from someone they know, email users would receive messages like, “Here is that document you asked for … don’t show anyone else ;-)”. Users would then open the attached document, usually named LIST.DOC. The malware then forwarded itself to the first 50 people in an infected user’s Microsoft Outlook address book, further spreading the infection in the process.
Remember the Melissa Virus! pic.twitter.com/xTjh47euKO
— Anon Heel (@AnonHeel) December 23, 2016
Think about that chain reaction for a second: Each infected computer had the ability to infect 50 more computers. On top of that, many of the email addresses found on people’s computers were actually groups of other email addresses, so it was often more than just one person being emailed.
Melissa had grave implications for company and web servers that carried the large volumes of emails being created. It successfully crippled hundreds of networks, including those of Microsoft and the United States Marine Corp. The New York Times reported in March 1999 that 250 organizations had called the Computer Emergency Response Team, a Pentagon-financed security service at Carnegie Mellon University, which meant that at least 100,000 workplace computers were affected. The final number infected was likely even higher than that.
A few days after the release of the virus, The Times spoke to Steve R. White, a senior manager of anti-virus research at the IBM Watson Research Center in Hawthorne, N.Y. He said that Melissa had “spread more widely and rapidly than any P.C. virus in history.”
1999: David Smith, the confessed author of the Melissa virus, pleaded guilty to computer crimes related to Melissa. He was released on bail and wasn’t sentenced for 29 months, receiving a 20 month sentence and $5,000 fine in 2002. pic.twitter.com/4cdeSu52zC
— Today In Infosec (@todayininfosec) December 10, 2018
What happened next?
Smith, Melissa’s creator, was arrested at his brother’s house following an investigation led by the FBI, the New Jersey State Police, who had help from others, including a Swedish computer scientist. They tracked him down electronically, just a week after the malware was released. Smith pleaded “not guilty” and said that he had no idea the virus would inflict this kind of damage. He claimed it was originally meant to be a harmless joke.
Two decades ago, computer viruses—and public awareness of the tricks used to unleash them—were still relatively new. The fast-moving and destructive Melissa virus changed that in a significant way. Learn more: https://t.co/D6HSThrAdG
— FBI (@FBI) March 25, 2019
“When I posted the virus, I expected that any financial injury would be minor and incidental. In fact, I included features designed to prevent substantial damage. I had no idea there would be such profound consequences to others,” he said in court, according to ZD Net.
The then-34-year-old ultimately served 20 months in jail and had to pay $5,000. The judge who oversaw his case also told Smith to stay away from computer networks or the internet unless authorized by the court. He could have faced up to five years in prison, but prosecutors suggested a lesser term when Smith agreed to help authorities find and thwart other viruses. Little can be found about what Smith is doing twenty years later, though he did appear to help the FBI for some time being released from his prison sentence.
The lasting impact of Melissa
Melissa may seem like a simple virus now, but the attack foreshadowed much of what was to come in the 21st century. As shown through the many recent data breaches of sensitive information (such as the attacks on Yahoo, the Democratic National Convention, Facebook, Paypal, Netflix, and more), cybercrime is one of the most threatening forms of crime of our current time.
Melissa also unfortunately inspired thousands of other malware attacks, including the Anna Kournikova, the Love Bug, Netsky and Bagle.
However, the unexpected is that Melissa made computer users more aware of what could be hacked and attacked — and forced both individual users and the federal government to deal with those possibilities.
In a statement given to the federal Subcommittee on Technology, Committee on Science, House of Representatives, Keith A. Rhodes, the technical director for Computers and Telecommunications Accounting and Information Management Division, listed the five major lessons learned from Melissa.
1. It showed how quickly computer viruses can rapidly increase.
2. Melissa showed how hard it is to trace viruses back to their source.
3. The virus showed how easily products can be exploited to attack their users.
4. It showed that there “are no effective agency and governmentwide processes for reporting and analyzing the effects of computer attacks.”
5. Finally, Melissa proved that computers can protect themselves from attacks when they are alerted to what is coming. Organizations who trained their employees and warned them against an imminent attack fared better than those who did not.
As shown through Rhodes’s statement, Melissa was a bit of a wake-up call. Awareness of the danger of opening unsolicited email attachments grew, along with the understanding of how much damage online viruses can do. Melissa showed the world how quickly computer viruses could spread and how vulnerable federal information systems are to computer attacks.
This article appeared in an InsideHook newsletter. Sign up for free to get more on travel, wellness, style, drinking, and culture..