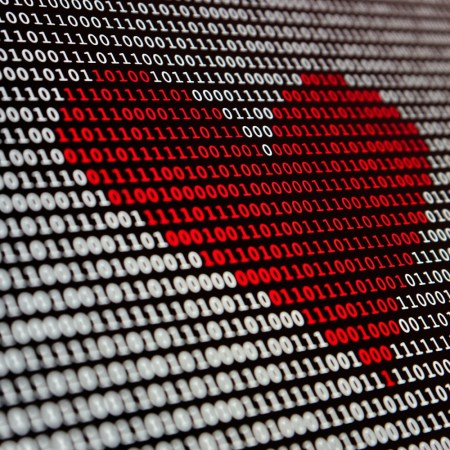
“Just what do you think you’re doing, Dave?”
Of all the sound bites and images from 2001: A Space Odyssey, the landmark sci-fi film that turns 50 this week, it’s HAL:9000 we remember best.
The sentient AI that maintained the Discovery One eventually malfunctioned, turned into a spy and killed a few astronauts before meeting its demise. (It was also kind of a dick.)
“All technology today could be a HAL 9000. Humans need to decide whether the tradeoff of technology abusing them is worth the benefits it provides,” says Dary Merckens, the CTO of Gunner Technology. “There was a tradeoff in 2001: technology got us to Jupiter, but also wanted to kill us. Which is the entire point of that movie — the progression of technology at three key stages in the history of humanity and our final push beyond technology and beyond the infinite.”
Before we get to the infinite, though, we must deal with the tech issues of today: Facebook data breaches, Alexa spying fears, runaway self-driving cars, the umpteenth warning that all your passwords were stolen.
So, below: What are the HALs of 2018? And how do we protect ourselves?
FACEBOOK
The fear: The social media giant is disseminating a lot of personal info about you to questionable third parties without your permission. Well, 87 million of you, at least.
Solution: If you want to keep Facebook, you can adjust your privacy settings. Or, you could #DeleteFacebook. But from there, you’ll also need to delete the apps that are accessing your FB account. And since the company can track you even after you delete your account, you’ll also need to block hundreds of URLs.
ALEXA
The fear: The voice assistant is always listening. And laughing at you. Also, you’re really gonna wanna read up on Amazon’s “voice sniffer algorithm” patent.
Solution: “Alexa is always recording and listening for the wake word to respond to your next request,” says Jason Miller, a CTO of 20 years. “To start, you should change the wake word from ‘Alexa’ to something else — this will help you from being unintentionally trolled (see South Park). And take advantage of the MUTE button on the device to prevent it from listening in at all, especially when you know you will not be engaging with it. Amazon keeps a complete history of what it hears, which you can access via the Alexa app. Periodically review these recordings and delete them as appropriate.”
INTERNET BROWSING
The fear: Wherever you go on the Internet, someone is tracking you. Which explains why you keep seeing the same ads over and over again.
Solution: “There are tools for your web browser that provide a higher level of privacy, such as using incognito option in Chrome or Safari’s ‘private window,’” explains Ralph Echemendia, the cybersecurity expert better known as the The Ethical Hacker. “There are also more off-the-record browsers like the TOR Browser. However, with the use of many of these tools, the speed or performance of your internet experience is reduced.” That said, a promising new web tool, 1.1.1.1, does promise to increase the privacy of your web browsing while speeding up your connection.
YOUR ONLINE IDENTITY
The fear: Your personal data and financial information was breached. See Equifax. Also, your passwords were compromised. See … well, every website you’ve ever used, but today let’s say Delta and Sears.
Solution: “Password managers can be useful and the use of passphrases and two-factor authentication will also reduce your risks online,” says Echemendia. While it might slow you down, we agree: for a great, secure password manager, we’re big fans of Dashlane.
YOUR WEBCAM
The fear: That built-in laptop camera is watching you. And so is your security cam.
Solution: Do what (surprise!) Mark Zuckerberg and the FBI do and cover that camera with tape. (muffle your computer’s mic while you’re at it). For security cameras, SimpliSafe founder/CEO Chad Laurans suggests looking for security cameras that have steel privacy shutters that click shut when you enter your home (which will disarm your security system).
PUBLIC WIFI
Your fear: Your info and browsing habits are far less safe in an airport or coffee shop.
Solution: “In general, if you can avoid using public wifi, you should,” says Holly Zink, a tech expert and writer for Digital Addicts Blog. “However, there are things you can do to protect your information. When using Gmail, make sure you have two-factor authentication. After using a public network, make sure you click ‘forget the network’ when you’re done, as there’s a chance a hacker may have a wifi network with a name similar to a local cafe. If you do use public wifi, make sure to double-check the name before connecting.” As well, you may want to look into using a VPN, which secures and anonymizes your online data.
DIGITAL EXTORTION
Your fear: Cyber criminals will hold your computer hostage until you pay up … a lesson Atlanta’s city government learned recently.
Solution: Beyond taking security measures before this happens, you’re probably screwed. “Depending on how valuable your data is to you, unfortunately, you usually must pay,” says Echemendia.
Finally, a few other pieces of advice that may help you in these troubled tech times:
Pass on location sharing: “Many devices and applications have default settings that share your location. This adds information and tags to posts and shares online. Turn this off wherever possible. Even most food delivery apps allow you to input your address, as opposed to sharing your location automatically.” — Sameer Somal, Co-founder/CFO at Blue Ocean Global Technology/Blue Ocean Global Wealth
Use a private keyboard: An app like Fleksy doesn’t transfer what you type to any outside servers or monitor your keystrokes.
Be aware of who’s tracking you: Here’s a comprehensive list of major tech companies that won’t delete your data.
Make some web noise: Instead of hiding your online self — which is increasingly harder to do — proactively fool those tracking sites with fake data by using a free plug-in like Noiszy.
Use one-time credit cards: The plug-in Privacy creates a virtual, disposable credit card number for every one of your online transactions. The transactions tie directly into your bank account, making each purchase more akin to a uniquely encrypted, one-time charge card purchase.
The Charge will help you move better, think clearer and stay in the game longer. Subscribe to our wellness newsletter today.